Whether you’re building your first home network or managing your own infrastructure, understanding networking fundamentals is crucial. This guide walks you through everything from choosing the right network topology to implementing robust security measures that protect your data.
Let’s start from the ground up and build your networking knowledge step by step.
Understanding Network Topologies
The way you arrange your network devices directly impacts performance, reliability, and cost. Network topology defines how your computers, servers, and other devices connect and communicate with each other.
Bus Topology: The Single Highway
In a bus topology, all devices connect to one central cable, so think of it like a main road where everyone shares the same path. It’s inexpensive and simple to set up, making it perfect for small networks or temporary setups. However, when traffic increases, this shared highway gets congested quickly. The biggest risk? If that main cable fails, your entire network goes down.
Star Topology: The Hub and Spoke Model
Star topology is what you’ll find in most modern offices and homes. Each device connects directly to a central hub or switch, creating a star pattern. This design makes troubleshooting much easier—if one computer has issues, it doesn’t affect the others. The central switch handles all the traffic management, and you can easily add new devices by plugging them into available ports.
The downside? Your central switch becomes a single point of failure. Invest in a quality switch with redundancy options if you’re running critical operations.
Ring Topology: The Circular Path
Devices in a ring topology connect in a circle, with data travelling in one direction (sometimes both with dual-ring setups). While this provides equal access for all devices, a break anywhere in the ring can disrupt the entire network unless you’ve implemented backup paths.
Mesh Topology: Maximum Redundancy
In mesh networks, every device connects to every other device. This creates multiple pathways for data, meaning if one connection fails, traffic reroutes through alternative paths. It’s expensive and complex to set up, but for mission-critical systems that can’t afford downtime, mesh topology delivers unmatched reliability.
How DNS Actually Works
When you type www.google.com into your browser, DNS (Domain Name System) works behind the scenes to translate that human-readable address into an IP address like 142.250.185.46 that computers understand.
Here’s what happens in those milliseconds:
- Your browser checks its local cache first
- If not found, your request goes to a DNS resolver (usually provided by your ISP)
- The resolver queries root nameservers, which direct it to the appropriate TLD (Top-Level Domain) server
- The TLD server points to the authoritative nameserver for that specific domain
- The authoritative server returns the IP address
- Your browser uses that IP to load the website
DNS Caching Speeds Everything Up
DNS caching stores query results temporarily, so the next time you visit that same website, your system already knows the IP address. This dramatically improves browsing speed and reduces server load.
Load Balancing: Distributing Traffic Intelligently
Imagine you’re running an online store during Black Friday. Thousands of customers are trying to access your site simultaneously. Without load balancing, your single server would crash under the pressure.
A load balancer sits between your users and your servers, distributing incoming traffic across multiple servers. This prevents any single server from becoming overwhelmed and ensures your application stays responsive even during traffic spikes.
Hardware vs Software Load Balancers
Hardware load balancers are physical devices operating at the network layer (Layer 3). They offer high performance and reliability but come with significant upfront costs.
Software load balancers run as applications at Layer 7 (application layer), giving you more flexibility in how you route traffic. You can make decisions based on URL paths, HTTP headers, or cookie values. Software load balancers are easier to deploy in cloud environments and cost less initially, though they may require more configuration.
Firewall Protection: Your Network’s Security Guard
Firewalls examine network traffic and decide what gets through based on security rules you define.
Packet-Filtering Firewalls
These operate at Layer 3, examining basic packet information like source IP, destination IP, and port numbers. They’re fast and efficient but provide only basic protection. Think of them as checking IDs at the door, so they verify who’s coming in but don’t inspect what they’re carrying.
Stateful Inspection Firewalls
Stateful firewalls operate at Layer 4 (Transport Layer) and track active connections. They understand the context of traffic, knowing whether a packet is starting a new connection or part of an existing conversation. This context awareness provides significantly better security than simple packet filtering.
IPv4 vs IPv6: The Address Space Evolution
We’re in the middle of a major internet transition. IPv4, the addressing system that’s powered the internet for decades, is running out of addresses.
IPv4’s Limitations
IPv4 uses 32-bit addresses, providing about 4.3 billion unique addresses. That sounds like a lot until you realize how many devices connect to the internet today: smartphones, tablets, smart home devices, IoT sensors, and more. We’ve exhausted the IPv4 address space, which is why we rely heavily on NAT (Network Address Translation) to share public IP addresses.
IPv6’s Solution
IPv6 uses 128-bit addresses, offering 340 undecillion (that’s 340 trillion trillion trillion) unique addresses. To put that in perspective, we could assign millions of IP addresses to every grain of sand on Earth and still have addresses left over.
Beyond the massive address space, IPv6 offers several improvements:
- No NAT required: Every device can have its own unique public IP address
- Built-in IPsec: Encryption and authentication are mandatory, not optional
- Simpler routing: More efficient packet headers reduce processing overhead
- Better for IoT: Devices can auto-configure without DHCP
- Improved mobile connectivity: Mobile devices can maintain connections as they move between networks
Dual-Stack: Running Both During Transition
Most networks today run dual-stack, supporting both IPv4 and IPv6 simultaneously. This allows IPv4-only devices and IPv6-only devices to coexist while we gradually transition. Your DNS resolver handles both address types, ensuring connections work regardless of which protocol a device uses.
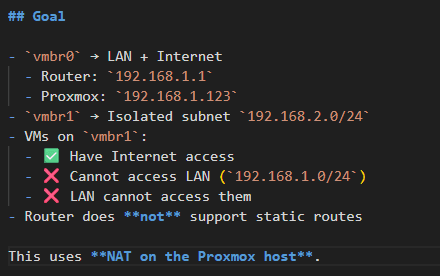
NAT: Extending IPv4’s Life
Network Address Translation (NAT) translates private IP addresses (like 192.168.1.100) used inside your local network into a public IP address when accessing the internet. This allows multiple devices on your home or office network to share a single public IP address, conserving the limited IPv4 address pool.
Subnetting: Dividing Networks Efficiently
Subnetting divides a larger network into smaller, more manageable sub-networks. This provides several benefits:
- More usable addresses through efficient allocation
- Enhanced security by isolating network segments
- Improved performance by reducing broadcast traffic
- Better organization grouping devices by department or function
Subnetting operates at Layer 3 of the OSI model and requires understanding subnet masks and CIDR notation. Once you grasp the concept, it becomes an invaluable tool for network design.
DHCP: Automatic Configuration
DHCP (Dynamic Host Configuration Protocol) automatically assigns IP addresses to devices joining your network. Instead of manually configuring each device, DHCP handles everything—IP address, subnet mask, default gateway, and DNS servers.
Dynamic vs Static IP Addresses
Dynamic IP addresses change over time and work perfectly for most devices like laptops, smartphones, and tablets. DHCP assigns these automatically.
Static IP addresses never change and are manually configured for servers, printers, and other devices that need consistent addresses for easy access.
Network Access Control Best Practices
Securing your network requires multiple layers of defense:
- Segment your network using VLANs to isolate different departments or device types
- Require strong authentication for all administrative access to routers and switches
- Use HTTPS instead of HTTP when accessing network device control panels
- Implement complex passwords and review them regularly
- Configure Access Control Lists (ACLs) to restrict traffic between network segments
Types of Networks You’ll Encounter
LAN (Local Area Network)
A LAN connects devices within a confined area, an office, building, or campus. Security measures include:
- Strong password-protected access control
- Firewalls monitoring and filtering traffic
- WPA2/WPA3 encryption for wireless networks
- IPsec for wired connections
- VLANs to isolate sensitive network segments
- Continuous monitoring to identify suspicious activity
WLAN (Wireless Local Area Network)
WLANs use Wi-Fi for connectivity. Enhanced security requires:
- WPA3 encryption protecting against brute-force attacks
- MAC address filtering restricting access to approved devices
- Regular firmware updates patching security vulnerabilities
VLAN (Virtual Local Area Network)
VLANs logically segment a physical network into isolated virtual networks. This is crucial for security:
- Isolate sensitive departments (HR, finance, R&D) from general network access
- Implement private VLANs preventing lateral movement within the same segment
- Use Layer 3 switches or firewalls to control and monitor inter-VLAN traffic
WAN (Wide Area Network)
WANs connect multiple LANs across large geographic areas through Internet Service Providers. Secure WAN connections using VPNs (Virtual Private Networks) to encrypt traffic over public internet connections.
Other Network Types
MAN (Metropolitan Area Network): Covers a city or metropolitan area with high-speed connectivity
PAN (Personal Area Network): Short-range connections for personal devices using Bluetooth or similar technologies
GAN (Global Area Network): Worldwide networks using satellites, undersea cables, and terrestrial infrastructure
CDN (Content Delivery Network): Geographically distributed servers delivering web content based on user location, reducing latency
P2P (Peer-to-Peer) Network: Decentralized architecture where each device can act as both client and server
Encryption and Security Protocols
Symmetric Encryption
Symmetric encryption (AES, DES, 3DES) uses the same key for both encryption and decryption. It’s fast and efficient but requires secure key distribution and management.
Asymmetric Encryption
Asymmetric encryption (RSA, ECC, DSA, PGP) uses key pairs, a public key for encryption and a private key for decryption. It’s more secure but slower than symmetric encryption.
Hybrid Encryption
Hybrid systems (SSL/TLS, SSH) combine both methods, using asymmetric encryption for secure key exchange, then symmetric encryption for data transfer. This balances security and performance.
Hashing
Hashing algorithms (MD5, SHA-1, SHA-256) create one-way functions perfect for verifying data integrity and securely storing passwords. You can’t reverse a hash to recover the original data, making it ideal for password storage.
Intrusion Detection and Prevention
IDS (Intrusion Detection System)
IDS passively monitors network traffic and alerts administrators to suspicious activities. It doesn’t block attacks, it just reports them.
Network-based IDS (NIDS) monitors all network traffic for malicious patterns Host-based IDS (HIDS) monitors individual machines for suspicious behavior
Popular tools include Snort and Suricata.
IPS (Intrusion Prevention System)
IPS actively blocks threats in real-time. When it detects malicious traffic, it can drop packets, terminate connections, or reconfigure network rules to prevent attacks.
Network-based IPS (NIPS) blocks malicious network traffic as it occurs Host-based IPS (HIPS) protects individual machines and blocks threats locally
Custom DNS Resolvers for Security
Custom DNS resolvers improve both security and performance:
- DNS filtering blocks known malicious websites before users can access them
- DNSSEC verifies DNS responses haven’t been tampered with, preventing DNS spoofing
- Private DNS avoids third-party logging and tracking, enhancing privacy
Network Analysis and Troubleshooting Tools
TCPDUMP
TCPDUMP captures and analyzes network packets in real-time. It’s essential for troubleshooting connectivity issues, identifying performance bottlenecks, and investigating security incidents.
GREP
GREP searches through text data for specific patterns, invaluable when analyzing log files or filtering command outputs during troubleshooting.
DDoS and Malware Protection
Preventing DDoS Attacks
- Rate limiting restricts the number of requests per user/system within defined time periods
- Traffic filtering using firewalls or IDS identifies and blocks abnormal traffic patterns
- Reverse proxies absorb traffic spikes and distribute requests across backend servers
Preventing Malware
- Network segmentation limits malware spread by containing infections to isolated segments
- User education about safe online practices prevents many infections
- Regular software updates patch vulnerabilities before malware can exploit them
- Antivirus software detects, quarantines, and removes malware
- DNS filtering blocks access to malicious websites hosting malware
Quality of Service (QoS) Optimization
Quality of Service (QoS) ensures critical applications receive the network resources they need. High QoS enables smooth video conferencing, lag-free gaming, and buffer-free streaming. Low QoS causes delays, buffering, and frustrating user experiences.
Key Metrics to Monitor
- Latency: The delay in data transfer
- Jitter: Variation in packet arrival times
- Packet Loss: Data packets failing to reach their destination
- Bandwidth: Your network’s data transfer capacity
Application-Specific Requirements
- VoIP requires low latency (under 150ms) for clear conversations
- Video streaming needs high bandwidth and consistent throughput
- File transfers can tolerate moderate delays but benefit from high bandwidth
QoS Techniques
Traffic shaping controls data flow to prevent network congestion during peak times
Prioritization assigns higher priority to critical traffic, VoIP gets priority over file downloads
Bandwidth reservation pre-allocates bandwidth for essential services ensuring they always have resources
Throttling reduces bandwidth for non-essential services during high-traffic periods
Packet scheduling and queuing ensures critical traffic is processed first, reducing latency for time-sensitive applications
Building Your Network: Where to Start
Start by assessing your specific needs:
- How many devices will connect to your network?
- What applications will run (file sharing, video conferencing, cloud services)?
- What are your security requirements?
- What’s your budget for equipment and ongoing maintenance?
- Do you need remote access capabilities?
Then implement these best practices progressively:
- Begin with a physical infrastructure (switches, routers, cabling)
- Implement proper segmentation using VLANs
- Configure firewalls and access controls
- Enable encryption for all sensitive data
- Set up monitoring and logging
- Establish backup and disaster recovery procedures
- Document everything thoroughly
- Train users on security best practices
Conclusion: Network Infrastructure is a Journey
Understanding network infrastructure isn’t just about memorizing protocols and configurations, it’s about building systems that are reliable, secure, and scalable. Whether you’re setting up a home office or managing enterprise networks, these fundamentals remain constant.
The networking landscape continues evolving. IPv6 adoption grows daily. New security threats emerge constantly. Cloud services change how we think about network architecture. Stay curious, keep learning, and don’t hesitate to experiment in test environments before deploying changes to production.
What networking challenge are you facing right now? Understanding these concepts gives you the foundation to tackle any network infrastructure project with confidence.
Further Reading:
- Cloudflare Learning Center – DNS
- AWS Networking Fundamentals
- GeeksforGeeks Networking Tutorials
- Cisco Networking Basics
Last updated: February 2026. Network infrastructure best practices and protocols are regularly updated. Always verify current security recommendations with official sources.