Every time you send an email, stream a video, or browse a website, your data travels through multiple network layers working together seamlessly. Understanding how these layers function is essential for anyone working with networks, troubleshooting connectivity issues, or building secure systems.
This guide breaks down the OSI (Open Systems Interconnection) model and the TCP/IP model that power modern networking. You’ll learn exactly how data moves from your application down to the physical cables and back up on the receiving end.
Why Network Models Matter
Before diving into the layers, let’s understand why these models exist. In the early days of networking, different manufacturers created incompatible systems that couldn’t communicate with each other. The OSI model was developed by the International Organization for Standardization (ISO) in 1984 to create a universal framework for network communication.
Think of network models like a postal system. Just as a letter goes through multiple steps (writing, enveloping, addressing, sorting, transporting, and final delivery), data travels through distinct layers, with each layer handling a specific function.
The OSI Model: Seven Layers Explained
The OSI model consists of seven layers, numbered from bottom to top. When you send data, it travels down these layers on your device and then up the layers on the receiving device.

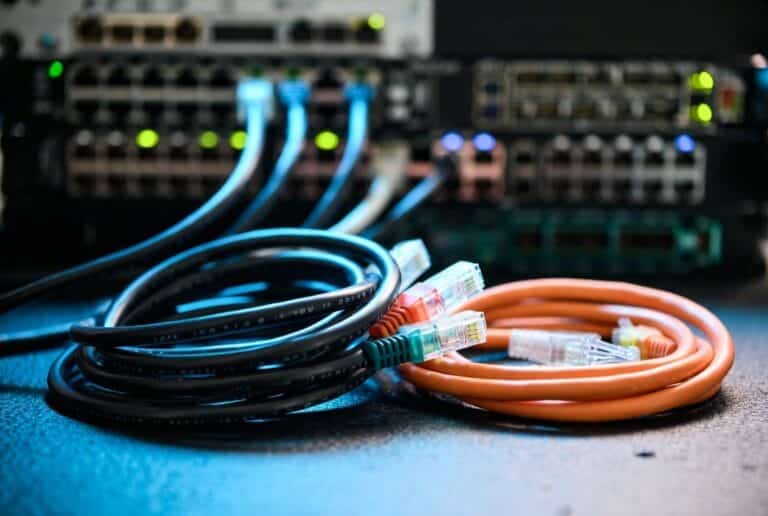
Layer 1: Physical Layer
The Physical Layer handles the actual physical connection between devices. It transmits raw bits (ones and zeros) over physical media like cables or wireless signals.
What operates at this layer:
- Network cables (Ethernet, fiber optic, coaxial)
- Hubs broadcast data to all devices without filtering based on MAC addresses
- Repeaters amplify signals to extend transmission distance and improve signal quality
- Modems connect to your Internet Service Provider (ISP), converting digital signals to analog and vice versa
- Wireless Access Points (WAPs) create WLANs (Wireless Local Area Networks) from wired connections
The Physical Layer defines specifications like voltage levels, transmission rates, cable types, and connector types. It’s concerned with the mechanical and electrical aspects of data transmission.
Layer 2: Data Link Layer
The Data Link Layer manages node-to-node data transfer on the same network. It handles physical addressing using MAC addresses and packages data into frames.
Key components at this layer:
- Address Resolution Protocol (ARP) maps IP addresses to MAC addresses
- Switches use MAC addresses to forward data to the correct destination within a network
- Bridges connect multiple network segments, forwarding data based on MAC addresses
- VLANs (Virtual LANs) segment a single physical network into multiple logical networks for better security and traffic management
This layer adds headers and trailers to create frames, performs error detection, and manages access to the physical transmission medium. It ensures data arrives correctly between directly connected devices.
Layer 3: Network Layer
The Network Layer handles routing packets across multiple networks. It manages logical addressing and determines the best path for data to travel.
Operations at this layer:
- Routers route packets between different subnets using routing tables and IP addresses
- IP Addresses provide unique logical addresses ensuring packets reach their intended destination
- Gateways translate and route data between different networks and protocols
- NAT (Network Address Translation) translates private IP addresses to public IP addresses for internet access
- VPN (Virtual Private Network) securely connects networks over the internet using encryption
The Network Layer adds IP addressing information to packets and makes routing decisions based on network congestion, priority, and the most efficient path available.
Layer 4: Transport Layer
The Transport Layer ensures reliable data transfer between devices. It segments data, provides error correction, manages flow control, and establishes connections.
Two main protocols operate here:
UDP (User Datagram Protocol):
- Connectionless: sends data without establishing a connection first
- Faster: no acknowledgments or handshakes required
- Unreliable: no error checking or guaranteed delivery
- Perfect for real-time applications like video streaming, online gaming, and VoIP where speed matters more than perfect accuracy
TCP (Transmission Control Protocol):
- Connection-oriented: establishes a connection before data transfer
- Reliable: guarantees correct delivery in the right order through acknowledgments
- Slower: higher overhead due to error checking and connection management
- Ideal for file transfers, emails, and web browsing where accuracy is critical
Additional Transport Layer functions:
- Port Forwarding directs incoming network traffic to specific devices or services within your LAN (common ports: 80 for HTTP, 443 for HTTPS, 5432 for PostgreSQL, 110 for POP3, 53 for DNS)
- Firewalls monitor and control traffic based on security rules
- Load Balancing distributes network traffic across multiple servers
- Flow Control manages data transmission rates to prevent network congestion
Layer 5: Session Layer
The Session Layer manages sessions or connections between applications. It establishes, maintains, and terminates communication sessions.
Key responsibilities:
- Session Management handles continuous data exchange between two devices and ensures data is properly synchronized
- Authentication ensures the session is secured and data is sent only between authenticated devices
- Checkpointing allows long data transfers to resume from the last checkpoint if interrupted rather than starting over
Think of this layer as the coordinator that keeps the conversation between two applications organized and synchronized.
Layer 6: Presentation Layer
The Presentation Layer formats data for the application layer. It acts as a translator, ensuring data is presented in a usable format.
Operations at this layer:
- Data Encryption protects data confidentiality using protocols like SSL/TLS
- Data Translation converts data between formats (JSON, HTML, XML, JPEG, ASCII)
- Data Compression reduces data size for faster transmission
- Character encoding ensures proper character set representation
This layer handles the syntax and semantics of the information exchanged between applications.
Layer 7: Application Layer
The Application Layer is the closest to you, the end user. It provides network services directly to applications.
Common protocols and their port numbers:
- HTTP (Port 80): Hypertext Transfer Protocol for transmitting web pages
- HTTPS (Port 443): Secure version of HTTP with encryption for secure web communication
- SSH (Port 22): Secure Shell for securely accessing remote devices
- FTP (Port 21): File Transfer Protocol for transferring files between client and server
- SFTP (Port 22): Secure File Transfer Protocol, an extension of SSH providing secure file transfer
- SMTP (Port 25): Simple Mail Transfer Protocol for sending emails between servers
- POP3 (Port 110): Post Office Protocol version 3 for retrieving emails, typically deleting them from the server after download
- IMAP (Port 143): Internet Message Access Protocol for accessing and managing emails on the server without downloading them
- DNS (Port 53): Domain Name System translates domain names to IP addresses
- DHCP (Ports 67, 68): Dynamic Host Configuration Protocol assigns IP addresses automatically to devices
These protocols define how applications communicate over the network, from browsing websites to sending emails to streaming videos.
The TCP/IP Model: Simplified and Practical
While the OSI model is comprehensive, the internet actually runs on the TCP/IP model, which was developed by the U.S. Department of Defense in the 1970s for ARPANET (the internet’s predecessor).
The TCP/IP model has four (or five, in updated versions) layers instead of seven. It’s more practical and less rigid than the OSI model.
TCP/IP Model Layers
1. Network Interface Layer (Physical + Data Link) Combines OSI Layers 1 and 2. Handles physical transmission and local network communication using Ethernet, Wi-Fi, and hardware addressing.
2. Internet Layer (Network) Corresponds to OSI Layer 3. Manages IP addressing, routing, and packet forwarding using IPv4 and IPv6 protocols.
3. Transport Layer Same as OSI Layer 4. Provides end-to-end communication using TCP for reliability or UDP for speed.
4. Application Layer (Session + Presentation + Application) Combines OSI Layers 5, 6, and 7. Handles all application-level protocols like HTTP, FTP, SMTP, and DNS.
OSI vs TCP/IP: Key Differences
The OSI and TCP/IP models differ in several important ways:
Number of Layers:
- OSI has 7 distinct layers
- TCP/IP has 4 (sometimes shown as 5) layers
Development Approach:
- OSI is a conceptual framework designed before implementation
- TCP/IP evolved from practical networking needs and real-world protocols
Protocol Dependency:
- OSI is protocol-independent (a theoretical reference model)
- TCP/IP is built around specific protocols (TCP, IP, UDP)
Usage:
- OSI is used for teaching and understanding networking concepts
- TCP/IP is what the internet actually uses
Specificity:
- OSI clearly separates functions into distinct layers
- TCP/IP merges related functions into fewer layers
Despite these differences, both models serve complementary purposes. Network professionals use OSI terminology to discuss and troubleshoot issues, but the actual protocols they work with follow the TCP/IP model.
How Data Flows Through the Layers
Let’s follow an email from your computer to a friend’s inbox to see these layers in action:
Sending the email (top-down):
- Application Layer: Your email client (Gmail, Outlook) prepares the message using SMTP
- Presentation Layer: The email is formatted, compressed, and encrypted
- Session Layer: A communication session is established with the mail server
- Transport Layer: TCP breaks the email into segments and adds sequence numbers
- Network Layer: Segments are packaged into packets with source and destination IP addresses
- Data Link Layer: Packets are framed with MAC addresses for the local network
- Physical Layer: Frames are converted to electrical signals and transmitted over the network cable or Wi-Fi
Receiving the email (bottom-up):
The process reverses. Physical signals become frames, frames become packets, packets become segments, segments are reassembled, the session is managed, data is decrypted and decompressed, and finally your friend’s email client displays the message.
Each layer adds its own header information during the journey down (encapsulation) and removes it on the way back up (decapsulation).
Wi-Fi Standards: Evolution of Wireless Networking
Wireless networking has evolved dramatically over the past two decades. Here’s what you need to know about Wi-Fi standards and security.
802.11a
- Frequency: 5 GHz
- Characteristics: Higher speeds but shorter range compared to 2.4 GHz
- Security: WPA, WPA2
802.11b
- Frequency: 2.4 GHz
- Characteristics: Longer range but lower speeds
- Security: WPA, WPA2
802.11g
- Frequency: 2.4 GHz
- Characteristics: Higher speeds than 802.11b while maintaining backward compatibility
- Security: WPA, WPA2
802.11n (Wi-Fi 4)
- Frequency: Both 2.4 GHz and 5 GHz (dual-band)
- Characteristics: Significantly better speeds and range through MIMO (Multiple Input Multiple Output) technology
- Security: WPA, WPA2, WPA3
802.11ac (Wi-Fi 5)
- Frequency: 5 GHz
- Characteristics: Dramatically higher speeds and improved performance, wider channels, and more spatial streams
- Security: WPA2, WPA3
802.11ax (Wi-Fi 6)
- Frequency: Both 2.4 GHz and 5 GHz
- Characteristics: Even better speeds, efficiency, and performance. Improved handling of many connected devices through OFDMA and better performance in crowded environments
- Security: WPA2, WPA3
Wi-Fi 6E
- Frequency: Extends Wi-Fi 6 into the 6 GHz band
- Characteristics: Provides more bandwidth, reduced latency, and faster speeds with less interference
- Security: WPA3 (mandatory for 6 GHz operation)
Wi-Fi 7 (802.11be)
- Frequency: 2.4 GHz, 5 GHz, and 6 GHz
- Characteristics: The latest standard offering even higher speeds, lower latency, and better reliability. Supports 320 MHz channels and enhanced Multi-Link Operation
- Security: WPA3 (mandatory for 6 GHz operation)
Wi-Fi Security: From WEP to WPA3
Wi-Fi security has evolved significantly to protect wireless networks from unauthorized access and eavesdropping.
WEP (Wired Equivalent Privacy) – Deprecated
The original Wi-Fi security protocol from 1997. It’s completely insecure and should never be used. Attackers can crack WEP encryption in minutes using freely available tools.
WPA (Wi-Fi Protected Access)
Introduced in 2003 as an interim solution while WPA2 was being developed. Uses TKIP (Temporal Key Integrity Protocol) encryption. Still vulnerable to attacks and should be avoided.
WPA2 (Wi-Fi Protected Access 2)
Introduced in 2004 and became the standard for over a decade. Uses AES (Advanced Encryption Standard) encryption with CCMP (Counter Mode with Cipher Block Chaining Message Authentication Code Protocol).
WPA2-Personal: Uses a pre-shared key (password) for authentication WPA2-Enterprise: Uses 802.1X authentication with a RADIUS server for larger organizations
While significantly more secure than WEP or WPA, WPA2 has known vulnerabilities including the KRACK (Key Reinstallation Attack) discovered in 2017.
WPA3 (Wi-Fi Protected Access 3)
WPA3 was announced in 2018 and addresses WPA2’s vulnerabilities while adding new security features.
Major WPA3 improvements:
Simultaneous Authentication of Equals (SAE) Replaces WPA2’s vulnerable pre-shared key exchange with a more secure method. SAE protects against offline dictionary attacks where attackers capture Wi-Fi traffic and try to crack passwords later.
Perfect Forward Secrecy Even if an attacker cracks your password, they can’t decrypt previously captured traffic. Each session uses unique encryption keys.
Protected Management Frames (PMF) Mandatory in WPA3, PMF protects against deauthentication attacks and other exploits targeting management frames.
Opportunistic Wireless Encryption (OWE) Provides encryption on open Wi-Fi networks (like coffee shops or airports) without requiring passwords, protecting against passive eavesdropping.
Stronger Encryption WPA3-Personal uses 128-bit encryption, while WPA3-Enterprise offers 192-bit encryption for highly sensitive environments like government and financial institutions.
WPA3-Personal vs WPA3-Enterprise:
- WPA3-Personal: For homes and small offices, uses SAE with a password
- WPA3-Enterprise: For businesses, uses 802.1X authentication with a RADIUS server and optionally 192-bit encryption
WPA3 Adoption Considerations
WPA3 is backwards compatible with WPA2 in transition mode, allowing older devices to connect. However:
- 6 GHz Wi-Fi (Wi-Fi 6E and Wi-Fi 7) requires WPA3. You cannot use WPA2 on the 6 GHz band
- Devices manufactured before 2018 likely don’t support WPA3
- Most devices from 2020 onwards support WPA3
- Check your router and device specifications for WPA3 compatibility
Setting up WPA3:
- Access your router’s admin interface (usually via web browser)
- Navigate to wireless security settings
- Select WPA3-Personal or WPA3-Enterprise
- For mixed environments, enable WPA3/WPA2 transition mode
- Save and restart your router
Practical Applications: Troubleshooting with Layer Models
Understanding network layers makes troubleshooting much easier. You can isolate problems to specific layers instead of checking everything.
Examples:
No internet connection:
- Layer 1: Check cables, verify lights on network equipment
- Layer 2: Verify switch configuration, check for MAC address conflicts
- Layer 3: Verify IP address assignment, test gateway connectivity
- Layer 4: Check if specific ports are blocked
- Layer 7: Test if specific applications work while others don’t
Slow network performance:
- Layer 1: Check for damaged cables or interference on wireless
- Layer 2: Look for broadcast storms or spanning tree issues
- Layer 3: Check for routing loops or suboptimal routes
- Layer 4: Investigate TCP window sizes and retransmissions
- Layer 7: Examine application-specific bottlenecks
Security incident:
- Layer 2: Check for ARP spoofing or MAC flooding
- Layer 3: Look for unusual routing or IP spoofing
- Layer 4: Examine port scans or SYN floods
- Layer 7: Investigate application-layer attacks like SQL injection
By thinking in layers, you quickly narrow down where problems originate and apply targeted solutions.
Network Devices and Their Layers
Different network devices operate at different layers:
Layer 1 (Physical):
- Hubs, repeaters, cables, connectors
Layer 2 (Data Link):
- Switches, bridges, wireless access points
Layer 3 (Network):
- Routers, Layer 3 switches, gateways
Layer 4 (Transport):
- Load balancers, firewalls (stateful inspection)
Layer 7 (Application):
- Application firewalls, proxy servers, content filters
Understanding these relationships helps you choose the right equipment and configure it properly.
Why Learn Both Models?
You might wonder why you need to learn both OSI and TCP/IP when the internet uses TCP/IP. Here’s why:
Use OSI for:
- Understanding networking concepts
- Communicating with other IT professionals (everyone knows “Layer 3” means networking)
- Troubleshooting (isolating problems to specific layers)
- Network certifications (CompTIA Network+, Cisco CCNA)
Use TCP/IP for:
- Understanding how the internet actually works
- Implementing real protocols
- Configuring network equipment
- Designing networks
Think of OSI as the theory and TCP/IP as the practice. Both are valuable.
Conclusion: Layers Power Everything
Every network interaction, from sending a text message to streaming 4K video, relies on these layered protocols working together. Data flows down through the layers on the sender’s side, travels across the network, and climbs back up the layers on the receiver’s side.
Understanding network layers gives you:
- Better troubleshooting skills
- Clearer communication with other IT professionals
- Knowledge to secure networks more effectively
- Foundation for advanced networking topics
Start applying this knowledge by observing your own network traffic. Use tools like Wireshark to see these layers in action. Check your Wi-Fi router settings to see which security protocols it supports. Experiment with different protocols and configurations.
The more you work with networks, the more intuitive these layers become. Soon you’ll instinctively know which layer to check when problems arise.
What networking challenge are you facing? Understanding these fundamental models gives you the framework to solve it.
Continue Learning:
- Cloudflare OSI Model Guide
- AWS OSI Model Explanation
- GeeksforGeeks OSI vs TCP/IP
- Fortinet Networking Resources
- Wi-Fi Alliance WPA3 Information
Last updated: February 2026. Network protocols and security standards evolve regularly. Always verify current best practices with official sources.